
Protection for URGENT/11 vulnerabilities Protect your VxWorks automation components against attacks and unauthorized access.
In July 2019, Armis Inc., an IoT security company, stated that they had discovered 11 zero-day vulnerabilities in VxWorks, the real-time operating system from Wind River. These vulnerabilities affect many industrial automation components. You can protect your network with mGuard security components.
What is VxWorks?
VxWorks is the most widely used real-time operating system and it is used on more than two billion devices. Typical areas of application include the aerospace and defense industries as well as machine control systems, medical equipment, and network infrastructure.
The 11 security vulnerabilities make it possible to spread malware within a network
URGENT/11
URGENT/11 is the name for 11 vulnerabilities that affect the VxWorks TCP/IP stack (IPnet), some of which remained undetected for up to 13 years. This means that they affect numerous versions of VxWorks. Six of the vulnerabilities are classified as critical, while the remaining five are classified as information leaks or logical errors.
The security vulnerabilities make it possible for attackers to take control of devices remotely with no user interaction required and to propagate malware into and within networks. Attackers are able to circumvent any firewalls and NAT solutions. Such an attack would be similar to the EternalBlue vulnerability, which was used to spread the WannaCry malware. Possible targets include SCADA systems, industrial controllers, firewalls, routers, printers, and even MRI machines.
The attack scenarios
In general, a distinction is made between three types of attack, depending on the location of the device in the network and the position of the attacker. However, in all three scenarios, the attacker can gain total control of the target device remotely and without any user interaction.
The second scenario involves an attack via an external network connection. The URGENT/11 vulnerabilities make it possible to take over devices with this type of connection undetected regardless of any firewall or NAT solutions.
Scenario 1: Attacking the network’s defenses
The first scenario is an attack on the network’s defenses, such as firewalls. However, if these firewalls use VxWorks, the URGENT/11 vulnerabilities make it possible for an attacker to launch a direct attack, taking full control over them and the devices that they are guarding.
Scenario 2: Attacking devices with external network connections
The second scenario involves an attack via an external network connection. The URGENT/11 vulnerabilities make it possible to take over devices with this type of connection undetected regardless of any firewall or NAT solutions.
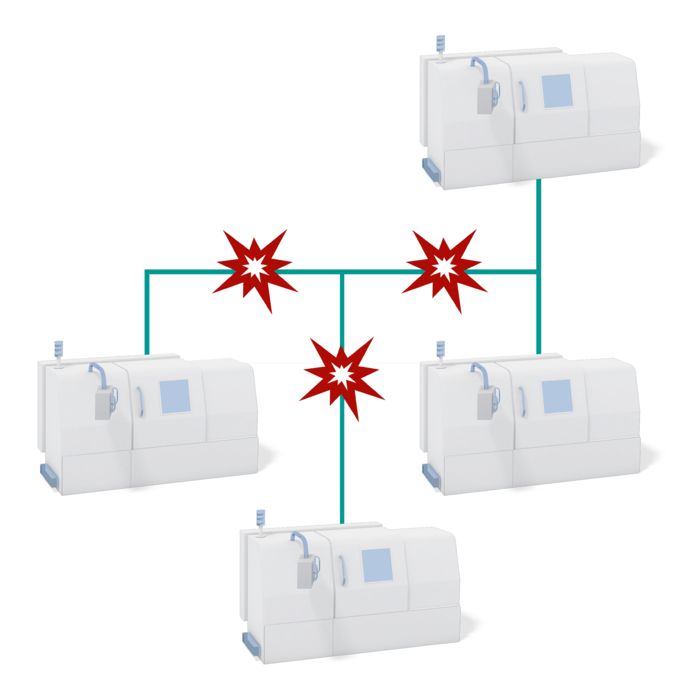
Scenario 3: Attacking from within the network
In the third scenario, attackers attack from within the network. As long as the attacker is already positioned within the network (for example as a result of a prior attack such as scenario 1 or 2), the URGENT/11 vulnerabilities allow them to take full control of devices with no user interaction required. This means that the attacker can broadcast malicious packets throughout the entire network, therefore infiltrating all of the devices in a production facility at once. This makes it possible, for example, to take control of an entire production line or even halt production completely.

mGuard security components protect your network
What can you do?
In general, updating all devices running VxWorks can be difficult and is, in some cases, not possible: first, all VxWorks devices must be identified, which can be a challenging task in itself. Furthermore, updates may not be available for all devices. And even if updates are available, installation can be a risky and time-consuming process, and you run the risk that the system will no longer work as expected afterwards.
Installing discrete security components such as mGuard security routers, which protect the network against known risks, is a much simpler solution. The mGuard devices are equipped with a function that blocks every TCP packet that contains an Urgent flag. The activation of this and additional security configurations in an mGuard security router provides comprehensive protection for VxWorks devices against exploitation of all six critical security vulnerabilities. Moreover, mGuard provides the same level of protection within a LAN as if it were operated in stealth mode. You can find further information on the configuration of an mGuard security router to protect against URGENT/11 vulnerabilities in the white paper below.
If you are unsure if this applies to you, or if you need help with implementation, please contact us. Our specialists will check your network and design an individual security concept for your system based on your requirements.
Do you want to find out more?
Download the white paper or find out more about our cybersecurity products.
