Safety meets security How to set up your machines safely: Find out about how to provide comprehensive, standard-compliant protection for your machinery.

The progressive digitalization and networking of machines and systems is leading to an increasing fusion of safety and security. In addition, crime on the Internet is becoming an ever-increasing threat potential for companies. A large number of companies have already registered cyberattacks with production downtimes. Cybercrime is therefore considered to be one of the biggest business risks.

New EU legislation Functional safety and cybersecurity come together
Regulatory developments in the European Union are currently being pursued to address this threat potential. In particular, the new Machinery Regulation, the Cyber Resilience Act, and the NIS2 are worth mentioning here.
The Machinery Regulation, which will be applied from January 20, 2027 onward, specifies EU-wide protection objectives for the design and construction of machinery. It takes new risks into consideration and adapts the security specifications to the current state of technological progress. The Cyber Resilience Act (CRA), on the other hand, protects consumers and companies that purchase or use digital products and software. As part of this, binding cybersecurity standards have been defined for manufacturers and dealers, and a CE marking has been specified for cybersecure products that are made available in the European Economic Area.
Functional safety and security can no longer be considered in isolation. They are complementary aspects of machine and system security. The security of machines and systems depends both on physical protective measures (safety) and on measures to prevent cyberthreats (security). A holistic approach that takes both aspects into consideration and uses synergies is promoted by the new Machinery Regulation and the Cyber Resilience Act.
Functional safety vs. cybersecurity How is cybersecurity differentiated from functional safety?
Functional safety represents the correct function of safety-related (control) systems and of other risk-mitigation measures. In this case, when a critical error occurs, the controller initiates the safe state. The requirements concerning the nature of safety-related control components are described in the type B standard EN ISO 13849 and the IEC 61508/IEC 61511/IEC 62061 series of standards. Depending on the degree of risk, corresponding risk-mitigation measures are classified into different safety levels: performance level (PL) or safety integrity level (SIL).
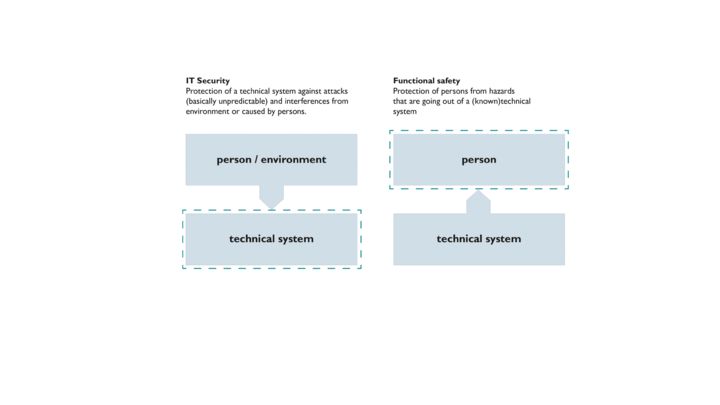
Vergleich zwischen Cyber Security und funktionaler Sicherheit
Cybersecurity, on the other hand, protects against attacks on the availability, integrity, and confidentiality of data. This is achieved through preventive or reactive technical and/or organizational measures. If one neglects the security aspects in the safety application, this can have direct consequences for production facilities. It can also have an indirect impact on the production process and therefore on the end product. Examples are pharmaceutical items or safety-relevant components for the automotive industry. Here, changes can have a significant negative impact on consumers.
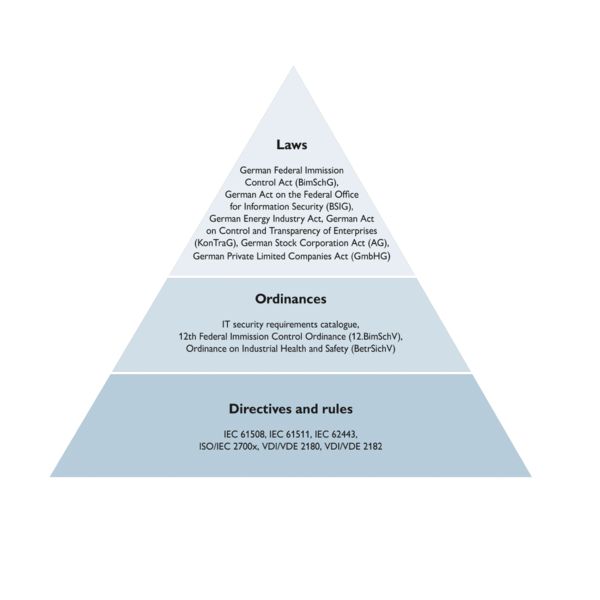
Overview of the relevant laws, ordinances, directives, and regulations

